Archives: Articles
-
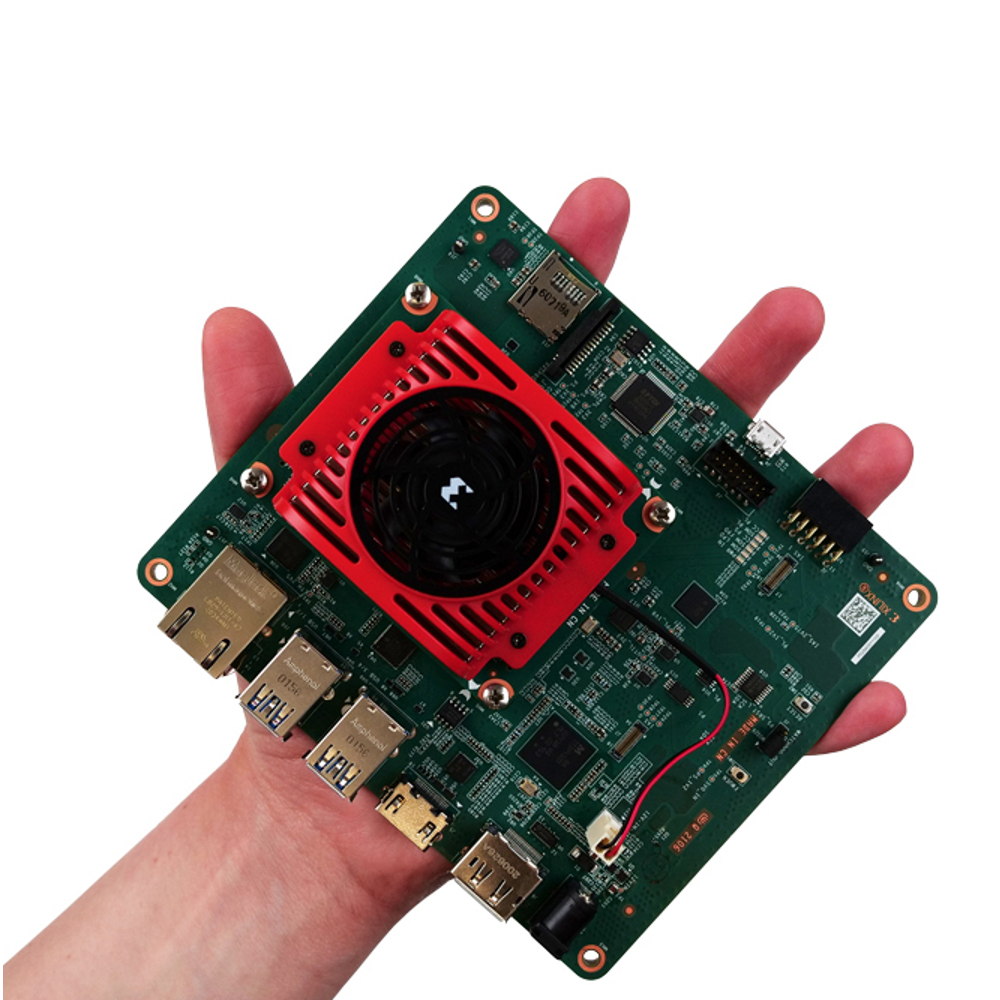
Xilinx Introduces Kria SoMs
Integration is the fundamental fuel that drives technical innovation. Each new node of Moore’s Law has allowed us to “Cram More Components” onto our integrated…
-

The First Emulators of Spring
It’s the season of rebirth. The sun is out. Flowers are in bloom. Birds busily build nests while semiconductor verification teams emerge from their long…