Archives: Articles
-
Hacking a Secure Air-Gapped Computer
Some security weaknesses would be hilarious if they weren’t so serious. And one man and his crack research team have found dozens of surprising ways…
-
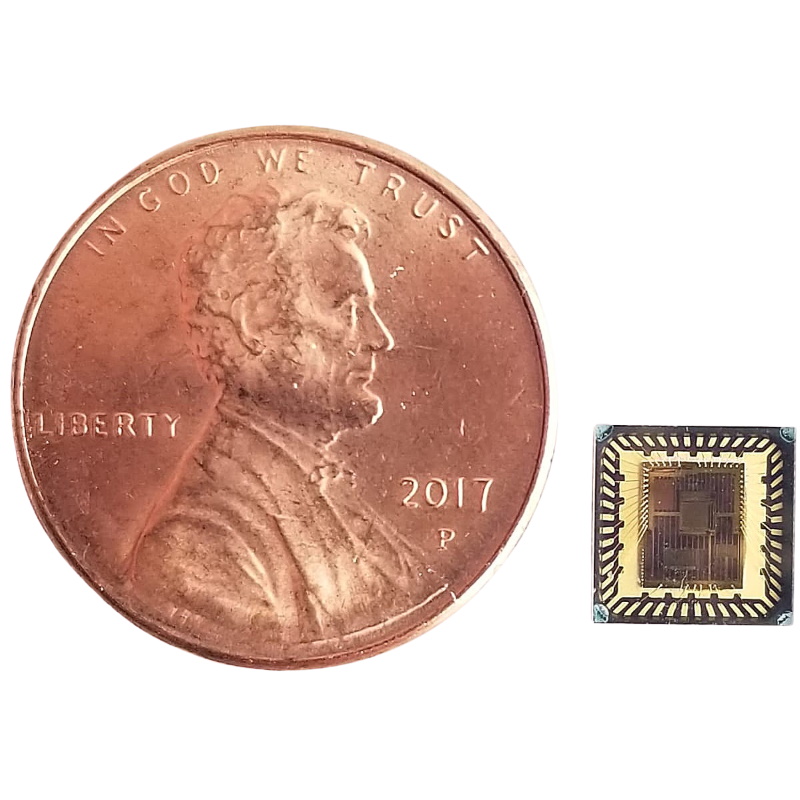
Neuromorphic Revolution
According to tech folklore, Carver Mead actually coined the term “Moore’s Law” – some ten years or so after the publication of Gordon Moore’s landmark…
-
Decapitating Malware with Content Disarm and Reconstruction (CDR) Technology
As you may imagine, I receive an eye-watering number of emails each and every day. To give you an idea as to the size of…
-

Contractually Obligated Year-End Article
“A ship in port is safe, but that’s not what ships are for.” – Grace Hopper You’re probably not reading this article. You’ve got better…
-
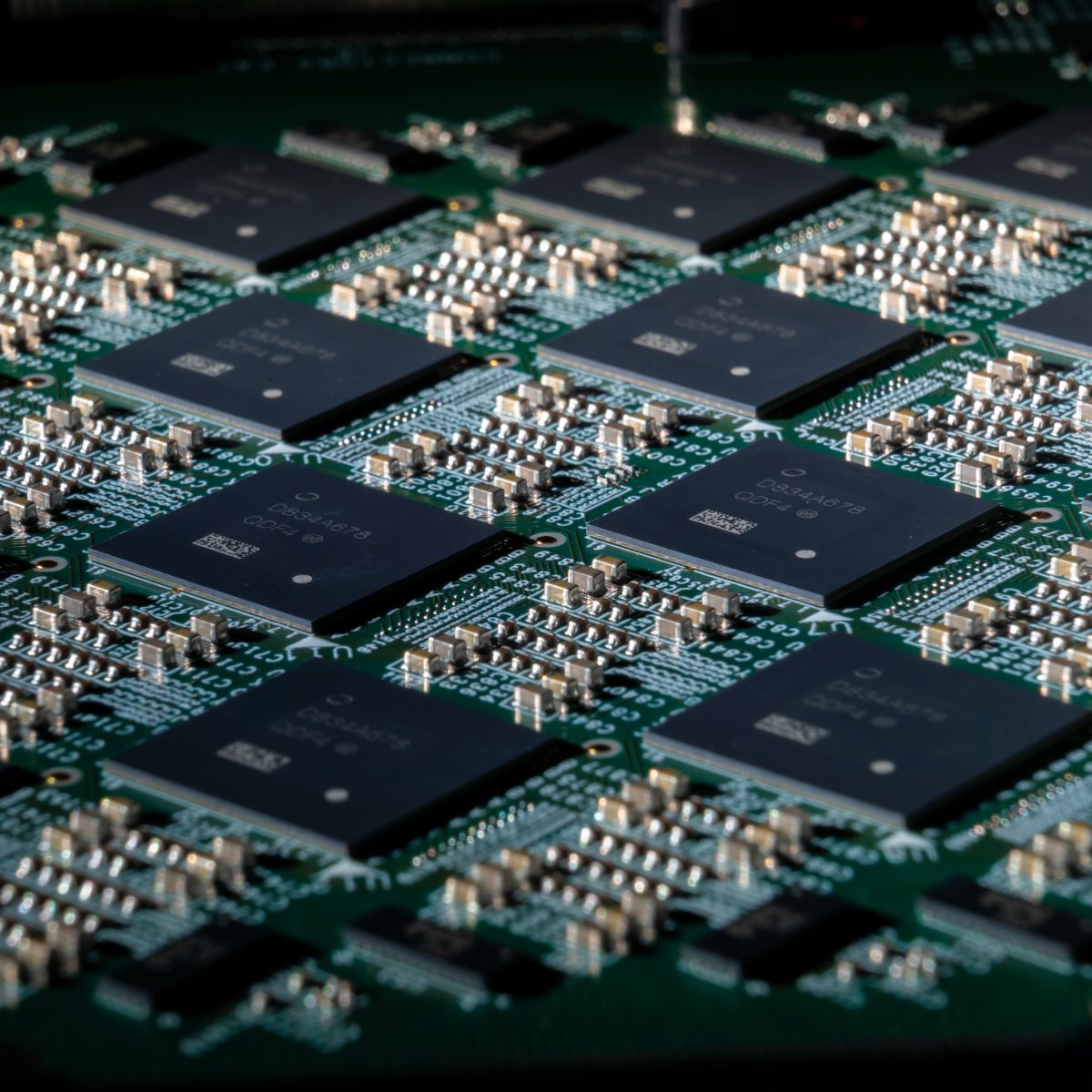
Esperanto AI Chip Exploits Thousands of Minions
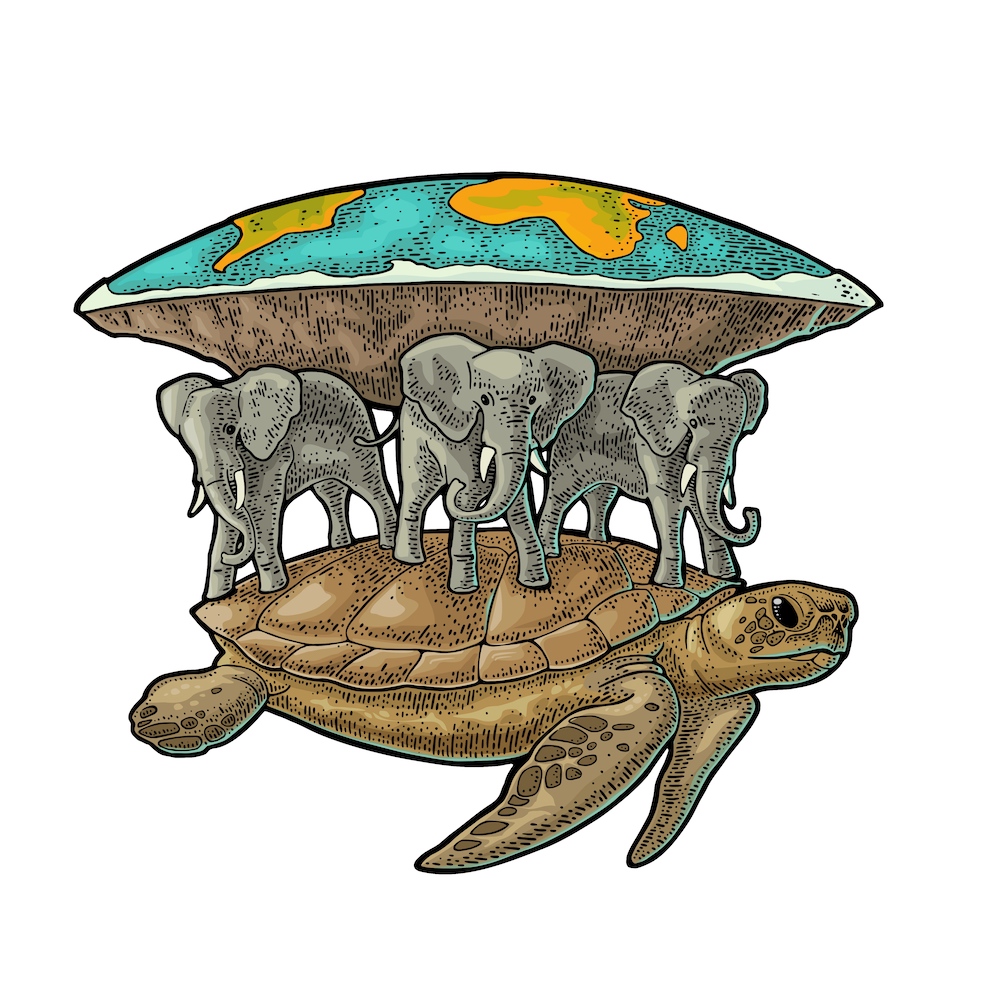
“The sad thing about artificial intelligence is that it lacks artifice and therefore intelligence.” – Jean Baudrillard It’s turtles all the way down. That’s the…
-

Lattice Launches Mach-NX
Pop Quiz – which FPGA company has sold the most devices? Nope, wrong. Guess again. And… wrong again. Neither Xilinx nor Altera/Intel, despite hovering around…